DARPA: Autonomous Bug-Hunting Bots Will Lead to Improved Cybersecurity
Relevant links are at the bottom of this post.
LAS VEGAS, Aug. 7, 2016 — This week, seven teams whose cyber reasoning bots played in the Defense Advanced Research Projects Agency’s Cyber Grand Challenge proved that machines by themselves could find and fix software safety problems in a simplified version of the code used everywhere, every day.
The world’s first all-machine hacking tournament wasn’t the answer to all cybersecurity problems, DARPA officials said, but it was a big step forward in a technical area where the Defense Department’s research arm aims to stir up a revolution.
The seven finalist teams represented an array of communities — academic pioneers from the field, security industry powerhouses and veterans of the capture-the-flag circuit. Each designed an innovative system that proved its skills during the CGC.
The competition played out in a parallel digital universe, as DARPA Program Manager Mike Walker recently characterized the stage holding 15 chilled air-gapped supercomputers running special software whose products were keenly observed by eight black-and-white-shirted highly expert referees.
Huge Strides
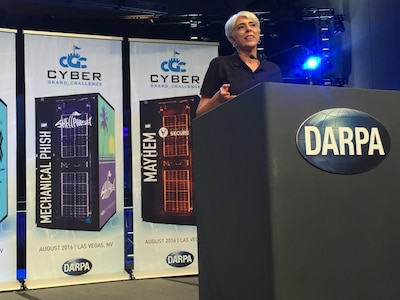
“Our mission is to change what’s possible so that we can take huge strides forward in our national security capabilities,” DARPA Director Arati Prabhakar said after the CGC. “And if that’s what our job is every single day, I think we did it today.”
The winners included ForAllSecure, a startup founded by a team of computer security researchers from Pittsburgh. The company placed first, winning a $2 million prize.
TECHx is a team of software analysis experts from GrammaTech Inc., a developer of software assurance tools and advanced cybersecurity solutions, and the University of Virginia in Charlottesville. Its second-place prize was $1 million. And Shellphish, a group of computer science graduate students at the University of California-Santa Barbara, won $750,000 as the third-place winner.
The other finalists are CodeJitsu, a team affiliated with the University of California-Berkeley. CSDS, a professor and a post-doctoral researcher from the University of Idaho in Moscow. DeepRed, a team of engineers from the Raytheon Company in Arlington, Virginia. And disekt, four people working out of a technology incubator in Athens, Georgia, who participate in capture-the-flag competitions worldwide.
The CGC was co-located this year with DEF CON, one of the world’s largest hacker conferences, and large portions of the massive audience in the Paris Hotel auditorium were hackers and other technical experts.
When Prabhakar spoke she described several of the agency’s more than 200 active programs and big ambitions, many of which she invited audience members to examine and participate in.
Big Ambitions and Cybersecurity
One of these was a new program she said would be DARPA’s next massive grand challenge — an effort called the Spectrum Collaboration Challenge.
“We’re going to challenge teams to build radio networks with embedded artificial intelligence that will allow each of those radio networks to dynamically scan and form hypotheses and predict what’s happening in radio spectrum,” she explained. By competing and collaborating with each other, the AI networks can dramatically advance the amount of capacity available from a fixed amount of spectrum, the director said..
Each one of DARPA’s big ambitions depends on cybersecurity, Prabhakar said.
“We can’t achieve these big dreams unless we can trust our data, trust our networks [and] trust the system that we are so completely reliant on today,” she said. “And because of that a revolution in cybersecurity is also a big ambition at DARPA today. Cyber Grand Challenge is a big part of that.”
Results are starting to come from the related DARPA portfolio, the director said, inviting the audience to engage with the agency and draw on fruits of the research.
“As we start developing this technology and as we start implementing it — ultimately, we hope, across the entire information ecosystem — as we do that we can start imagining a future where we actually have some foundation of cybersecurity,” Prabhakar said.
“Not invulnerability,” she added, “but we can live in a future where we can get on with the business of insuring the fruits of this phenomenal information revolution that we’re all dependent on today.”
Earning Its Place
In Walker’s remarks he went back to 2005, recalling Stanley, the self-driving car that won the 2005 DARPA Grand Challenge.
Stanley was a future technology prototype and a research and engineering milestone, but not a particularly good self-driving car by today’s standards, Walker said, noting that it was filled with computing, sensing and communications gear and couldn’t drive on streets or handle traffic.
All the same, he said, “Stanley earned its place in the Smithsonian by redefining what was possible. And today the technology descended from Stanley and his competition are driving on America’s streets all on their own. That long-awaited revolution is arriving on our streets and highways right now.”
The CGC prototypes are just like Stanley, Walker said.
They work only on a very simple research operating system and spend a huge amount of computing power to think about the security problems of small example services. The complex bugs they found during capture the flag are impressive, but they’re not as complex as real-world bugs, he added, and a huge amount of engineering must be done before such prototypes could guard the networks in use today.
“I invite you this weekend to imagine the technology that will follow these first prototypes and what that technology will mean,” Walker said. “Imagine networks where zero day cannot happen to anybody, where zero day does not guarantee a hacker’s success, where defenders work together with guardian machines to keep networks safe.”
“Imagine getting a text message from the system that protects your business, letting you know it just learned about a new flaw in your document reader and synthesized a new patch all on its own,” he said. “It’s coming, and we have these three days to imagine it together.”

Military applications for systems that emerge from these prototype machines will be the same ones that affect commercial off the shelf software from major vendors, which is what DoD buys, Walker said.
“The ability for commercial off-the-shelf software to be defended in the ways that I’ve described previously as the result of an open-technology revolution that occurs, we benefit along with everyone else,” he added.
Common Ground
With the audience, Walker briefly discussed formal verification, the field in which the security properties of native code are accompanied by a mathematical proof, and a DARPA-funded open-source technology that is a formally verified control system for a commercially available quadcopter.
“The research community behind this code believes that formal verification provides powerful promises about the absence of entire classes of flaws,” he said, “and we’d love to hear from you about how strong this security really is. We also hope in the future to call for new frontiers to formal verification.”
Next, Walker recalled a 2010 DARPA program called Cyber Fast Track whose program manager was network security expert and hacker Peiter Zatko, also known as “Mudge.” The program offered alternatives to government contracts for security work by hackers and similar experts.
“All of that technology development happened because Mudge became the first person from this hacker community to come to DARPA to be a program manager,” Walker said, noting that he went to a lot of Mudge’s Cyber Fast Track talks and was inspired by the common ground that he forged between DARPA and the hacker community.
“I’m proud today to be following in the tradition he started,” Walker said, adding that some in the audience might be wondering if they could build their vision of future technology at DARPA.
“Mudge started a tradition of hacker program management at DARPA and it’s my sincere hope that as my term limit ends and I leave the agency that some of you will step up to continue this tradition,” Walker said. “Until it’s easy to write defensible code and networks are secure by default, there must always be hackers working at DARPA to create … shared technology.”
He asked interested audience members to get in touch if they “have a technology vision, the ability to lead teams and an aptitude for public service.”
http://www.defense.gov/News/Article/Article/907045/darpa-autonomous-bug-hunting-bots-will-lead-to-improved-cybersecurity
